Device Identification

In this project, we study remote device identification in wireless and wireline networks and its implications on the security of multi-hop wireless and peer-to-peer wireline networks. This project is funded by the Zurich Information Security Center (ZISC).
The following is a list of publications made in this project:
On Physical-layer Identification of Wireless Devices: We present a systematic review of physical-layer identification systems and provide a summary of current state-of-the-art techniques. We further present a classification of attacks and discuss the feasibility, limitations, and implications in selected applications. We also highlight issues that are still open and need to be addressed in future work.
On The Practicality of UHF RFID Fingerprinting: How Real is the RFID Tracking Problem? We build and deploy a low-cost RFID fingerprinter to extract fingerprints from UHF RFID tags. Considering an example Shopping Mall scenario, we show that this portable setup can enable people tracking.
Physical-layer Identification of UHF RFID Tags: We evaluate several techniques for the extraction of physical-layer fingerprints from UHF RFID tags. We show the implications on tag holder privacy and tag cloning in RFID-enabled supply chains.
Attacks on Physical-layer Identification: We study the feasibility of performing impersonation attacks on the modulation-based and transient-based device identification techniques. We show that both techniques are vulnerable to impersonation attacks.
Physical-layer Identification of RFID Devices: We propose several techniques for the extraction of RFID physical-layer fingerprints. We show that RFID transponders can be accurately identified based on their physical-layer properties.
Transient-based Identification of Wireless Sensor Nodes: We propose a novel transient-based identification method and analyze its performance in terms of various parameters. We also study the feasibility of certain types of attacks on the proposed techniques.
Implications of Radio Fingerprinting on the Security of Sensor Networks: We demonstrate the feasibility of fingerprinting the radio of wireless sensor nodes.
Syssec members on the project:
- Boris Danev, Davide Zanetti and Srdjan Capkun
Former members:
- Thomas S. Heydt-Benjamin, Kasper Bonne Rasmussen
On Physical-layer Identification of Wireless Devices
We present a systematic review of physical-layer identification systems and provide a summary of current state-of-the-art techniques. We further present a classification of attacks and discuss the feasibility, limitations, and implications in selected applications. We also highlight issues that are still open and need to be addressed in future work.
Related work:
- Boris Danev, Davide Zanetti, Srdjan Capkun
On Physical-layer Identification of Wireless Devices
In ACM Computing Surveys (ACM CSUR), 2012 [DownloadPDF (PDF, 378 KB)vertical_align_bottom | Downloadbibtex (BIB, 281 Bytes)vertical_align_bottom]
On The Practicality of UHF RFID Fingerprinting: How Real is the RFID Tracking Problem?
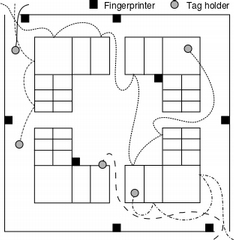
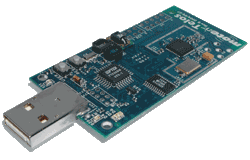
In this work, we demonstrate the practicality of people tracking by means of physical-layer fingerprints of RFID tags that they carry. We build a portable low-cost USRP-based RFID fingerprinter and we show, over a set of 210 EPC C1G2 tags, that this fingerprinter enables reliable identification of individual tags from varying distances and across different tag placements (wallet, shopping bag, etc.). We further investigate the use of this setup for clandestine people tracking in an example Shopping Mall scenario and show that in this scenario the mobility traces of people can be reconstructed with a high accuracy.
Related publication:
- Davide Zanetti, Pascal Sachs, Srdjan Capkun
On The Practicality of UHF RFID Fingerprinting: How Real is the RFID Tracking Problem?
In Proceedings of the 11th Privacy Enhancing Technologies Symposium (PETS), 2011 [DownloadPDF (PDF, 455 KB)vertical_align_bottom | Downloadbibtex (BIB, 270 Bytes)vertical_align_bottom]

Physical-Layer Identification of UHF Tags
In this work, we study physical-layer identification of passive UHF RFID tags. We show that, based on timing features of the signals, UHF RFID tags can be classified, independently of the location and distance to the reader (tested up to 6 meters), with an accuracy of approx. 71%. Additionally, we show that is possible to uniquely identify a maximum of approx. 2^6 UHF RFID tags independently of the population size. We analyze the implications of these results on tag holder privacy. In controlled environments, UHF RFID tags can be uniquely identified based on their signal spectral features with an Equal Error Rate of 0%; we discuss the application of those techniques to cloning detection in RFID-enabled supply chains.
Related publication:
- Davide Zanetti, Boris Danev, Srdjan Capkun,
Physical-layer Identification of UHF RFID Tags
In Proceedings of the ACM MobiCom (Annual International Conference on Mobile Computing and Networking), 2010 [DownloadPDF (PDF, 665 KB)vertical_align_bottom | Downloadbibtex (BIB, 362 Bytes)vertical_align_bottom | Downloadposter* (PDF, 788 KB)vertical_align_bottom]
* Poster presented at the USENIX Security Symposium, 2010.
Attacks on Physical-Layer Identification
This work studies the feasibility of performing impersonation attacks on the modulation-based and transient-based identification techniques. Both techniques are vulnerable to impersonation attacks; however, transient-based techniques are reproducible with a higher difficulty due to the effects of the wireless channel and antenna in their recording process. We assess the feasibility of performing impersonation attacks by extensive measurements as well as by simulations using collected data from wireless devices. We discuss the implications of our findings and how they affect current device identification techniques and related applications.
Related publication:
- Boris Danev, Heinrich Luecken, Srdjan Capkun and Karim El Defrawy,
Attacks on Physical-layer Identification,
in Proceedings of the ACM WiSec, 2010 [DownloadPDF (PDF, 225 KB)vertical_align_bottom | Downloadbibtex (BIB, 367 Bytes)vertical_align_bottom]
Physical-Layer Identification of RFID Devices

We propose several techniques for the extraction of RFID physical-layer fingerprints. We show that RFID transponders can be accurately identified in a controlled environment based on stable fingerprints corresponding to their physical-layer properties. We tested our techniques on a set of 50 RFID smart cards of the same manufacturer and type, and we show that these techniques enable the identification of individual transponders with an Equal Error Rate of 2.43%. We further applied our techniques to a smaller set of electronic passports, where we obtained a similar identification accuracy. Our results indicate that physical-layer identification of RFID transponders can be practical and thus has a potential to be used in a number of applications including product and document counterfeiting detection.
Related publication:
- Boris Danev, Thomas S. Heydt-Benjamin, Srdjan Capkun,
Physical-layer Identification of RFID Devices,
in Proceedings of the USENIX Security Symposium, 2009, [DownloadPDF (PDF, 913 KB)vertical_align_bottom | Downloadbibtex (BIB, 362 Bytes)vertical_align_bottom]
Transient-Based Identification of Wireless Sensor Nodes
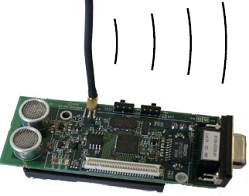
We propose a novel technique for transient-based identification and show that it enables reliable and accurate identification of identical (same model and manufacturer) sensor nodes with an Equal Error Rate as low as 0.0024 (0.24%). We analyze the identification accuracy of our system in terms of number of signals used to build the device fingerprint, ditance, antenna polarization, voltage and temperature. We also study the feasibility of a number of attacks on the identification system.
Related publication:
- Boris Danev, Srdjan Capkun,
Transient-based Identification of Wireless Sensor Nodes,
in Proceedings of ACM/IEEE IPSN, 2009, [DownloadPDF (PDF, 446 KB)vertical_align_bottom | Downloadbibtex (BIB, 5 KB)vertical_align_bottom]
Implications of Radio Fingerprinting on the Security of Sensor Networtks
We demonstrate the feasibility of fingerprinting the radio of wireless sensor nodes (Chipcon 1000 radio, 433MHz). We show that, with this type of devices, a receiver can create device radio fingerprints and subsequently identify origins of messages exchanged between the devices, even if message contents and device identifiers are hidden. We further analyze the implications of device fingerprinting on the security of sensor networking protocols, specifically, we propose two new mechanisms for the detection of wormholes in sensor networks.
Related publication:
- Kasper Bonne Rasmussen, Srdjan Capkun,
Implications of Radio Fingerprinting on the Security of Sensor Networks,
in Proceedings of IEEE SecureComm, 2007, [DownloadPDF (PDF, 262 KB)vertical_align_bottom | Downloadbibtex (BIB, 242 Bytes)vertical_align_bottom]
